Secure Erase for SSDs Helps Sanitize Data and Boost Efficiency
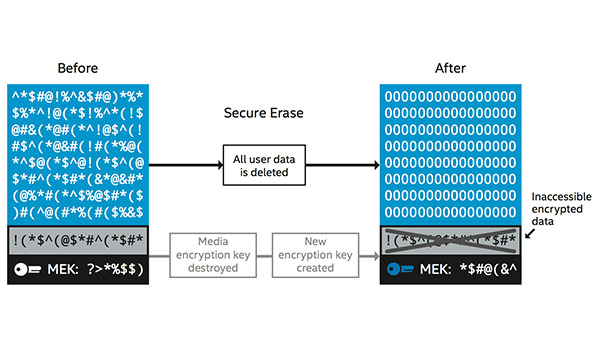
IT Best Practices: Protecting data is one of Intel IT’s most important duties to the enterprise. And the practice of protecting data includes not only data that is actively being used, but also data that needs to be erased when repurposing or disposing of PCs. Intel IT uses secure erase because it is the most effective way to sanitize data on an Intel Solid State Drive (Intel SSD). We have validated secure erase through internal testing and third-party testing and have approved its use in place of techniques traditionally used with hard disk drives (HDDs).
Our technicians wipe the data from approximately 20,000 SSDs every year. Secure erase enables technicians to securely wipe a self-encrypting Intel SSD in just seconds. The legacy drive wipe processes involved a three-pass overwrite and could take hours (five or more hours for large drives) and required costly specialized software licenses and equipment. Because the secure erase process is simple and fast, wipe verification and technician training are also simplified. We believe the Intel SSD Professional Family offers the best approach for storing and protecting corporate data and employees’ personally identifiable information and that secure erase is the best method for protecting data when it is no longer needed.
For more information on Intel IT Best Practices, please visit intel.com/IT
Posted in:
Intel, Intel IT, IT White Papers, IT@Intel, Security































