Taking enterprise security beyond the edge
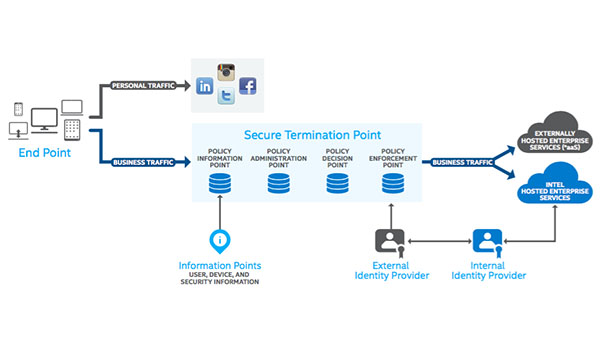
IT Best Practices: Intel IT is developing a beyond-the-edge security strategy that will enhance security in our environment. This new strategy addresses several drawbacks with today’s approach to security.
For more information on Intel IT Best Practices, please visit intel.com/IT
Posted in:
Cloud Computing, Information Technology, Intel, Intel IT, IT White Papers, IT@Intel































