IT Business Review: Striking a balance between protection and enablement
 |
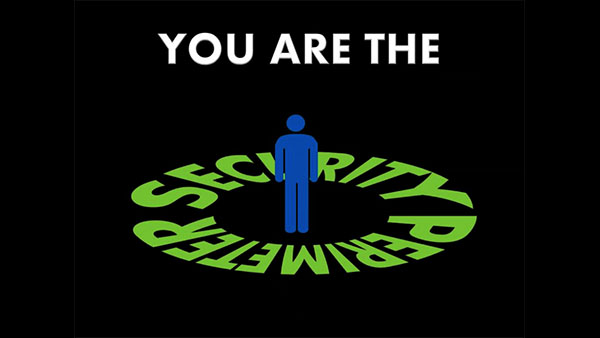
IT Best Practices: Information security has traditionally revolved around keeping the “good guys” in and the “bad guys” out. Taking a page from the medieval playbook, security professionals have tirelessly built higher virtual walls, deeper digital moats, and more capable [See the full post…] |
|
|